Third Party Risk Management (TPRM) Service
Reliance on third party business relationships including cloud service providers continues to grow. And contractual obligations now typically require adherence to defined cybersecurity standards. Every business is responsible for managing risks from third party business relationships to protect against breaches of sensitive or personal information that directly impact reputation, profitability, compromise regulatory compliance, and raise potential for litigation. KLC Consulting can help you create a third party risk management (TPRM) program from development stage to performing vendor risk assessments. We also provide guidance in helping you manage your third-party relationships with a SaaS-based risk management platform.
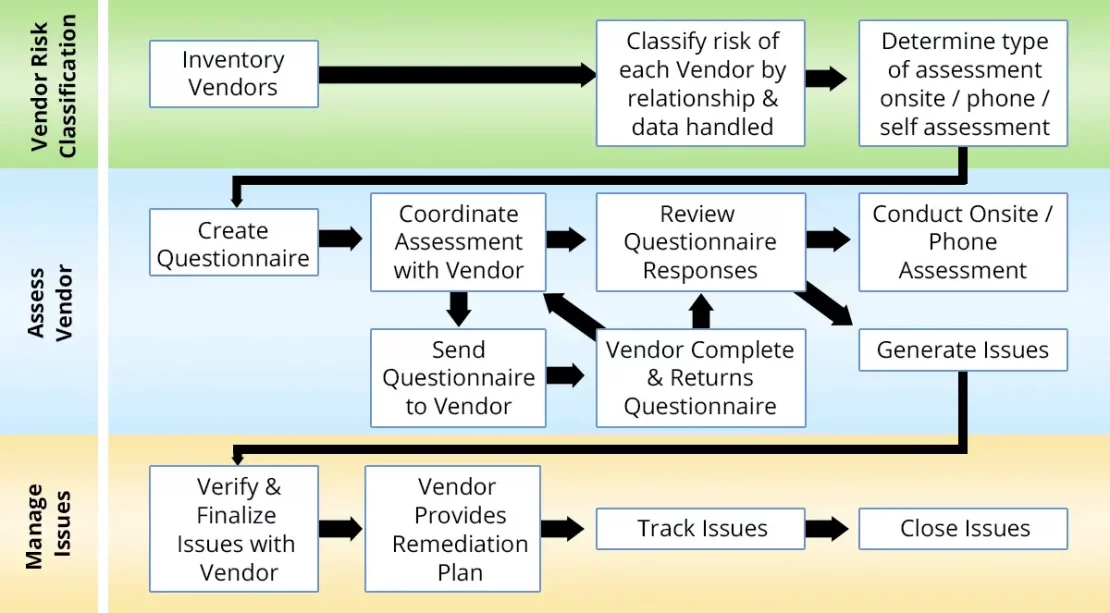
Our approach to Vendor Security Risk Management and Assessment
Our TPRM approach begins with onboarding and scoping, interviews with key stakeholders, a review of documents, and a comparison of your program with best practices. We identify your key vendors and degree of cyber risk based on a supplier risk maturity model and our framework for best practices. Our deliverable report shows findings based on criticality and a plan for remediation that embraces your budgetary constraints.
- Define vendor relationships and compliance requirements
- Collect vendor data via questionnaire and perform vendor security review
- Evaluate vendor security practices using ISO/IEC 27001/27002 Security techniques and code of practice for information security management
- Generate vendor report including executive summary, issues and recommendation
- Track vendor issue resolution and follow-up