We’re a CMMC Consultant who provides CMMC help. This CMMC Consulting Video features the latest information about CMMC: POAMs, bifurcation, flow down requirements, COTS, Incident Response Reporting, and DFARS requirements
Introduction
[Paul] Hi, I’m Paul Casassa, Director of Operations with KLC Consulting. Today, I’m conversing with Kyle Lai, our President and CISO of KLC Consulting. Let’s talk about how the changes in CMMC affect our CMMC Consulting services. How are you doing today, Kyle? [Kyle] Great, how are you doing, Paul?CMMC Consulting and CMMC 2.0
[Paul] I’m well, thank you. So, Kyle CMMC 2.0 was released by the DoD back in November 2021, if that’s correct, right? So, if we can, why don’t we go through some of the high-level changes that our audience. The defense industrial base companies would be interested in knowing to plan for the changes. Incorporate them into their plans to engage a CMMC consultant?Highlights of CMMC 2.0 changes
[Kyle] Sure, yeah, from CMMC 1.0 to 2.0, the DoD originally had 130 practices. However, CMMC 2.0 eliminated the delta 20, the additional 20 controls on top of NIST 800-171. So, now it is 100 percent mapped to NIST 800-171. And now, there are only 110 practices or controls. They eliminated the maturity processes.Five maturity levels reduced to three
There were initially five different levels: level one to level five. Levels two and four were never really used. So now, with CMMC 2.0, level one is still level one, and level three is the new level two. And the old level three is the new level three. So, there are only three levels in the new CMMC 2.0: one, two, and three.
CMMC Consulting: Plan of Action and Milestones now allowed
And also, one of the significant differences is that CMMC 1.0 did not allow a POAM. A “Plan Of Action and Milestones.” Meaning that you cannot have any gaps before you can get the certification. CMMC 2.0 allows for some limited Plan Of Action and Milestones or gaps. They give you 180 days to close the gaps; however, you cannot have the high-risk practices in your POAM. And these are just some of the highlights of the changes affecting CMMC and our CMMC consulting.
CMMC Maturity Levels Explained
[Paul] Okay, well, thanks for that, Kyle. So, maybe you could cover the different levels and who falls into the different levels. For example, what level speaks to FCI “Federal Contract Information”? What level speaks to CUI or “Controlled Unclassified Information”? It would be helpful to know in planning for CMMC Consulting and compliance. [Kyle] Yeah. So, if you handle Federal Contract Information, you are required to be CMMC level one. It’s is a self-assessment. If you are handling CUI or “Controlled Unclassified Information,” you must be at level two. A minimum of level two, and possibly level three.When CMMC 2.0 becomes effective
[Paul] You had indicated that CMMC 2.0 was released back in November of last year. When does it become effective? [Kyle] CMMC 2.0 should become finalized after the DoD completes its Rulemaking. It should be around the end of 2022 or the beginning of 2023. The DoD – they’re going to take about nine to 24 months to do their Rulemaking. And they are going to make changes to two of the rules: one is 32 CFR; the other is 48 CFR. But 48 CFR won’t happen until after 32 CFR. So, they’re going to take about nine to 24 months. I estimate that they’re going to be closer to the 24-month mark. So, end of 2022 or beginning of 2023, that’s my guess.Kyle’s recommendations during the rulemaking period
[Paul] Okay, and what’s your recommendation, there’s some time before this becomes effective. And defense industrial base companies need to be pursuing it. What is your advice on what they should be doing in the meantime, between now and then? Pursue CMMC Consulting options (hire a CMMC consultant)?Pursue DFARS 252.204-7012 compliance
[Kyle] So, the organizations seeking these certifications. If you are looking for CMMC level two because you handle CUI, you should start the process as soon as possible. It will take time for you to become compliant with NIST 800-171. And also, remember that DFARS 252.204-7012 is a requirement that became official on December 31, 2017. And that means that all the non-federal organizations. The federal contractors and the DoD contractors that handle controlled unclassified information or CUI must comply with NIST 800-171. They must do a self-assessment and also put together an incident response plan. A reporting plan so they can report incidents within 72 hours of discovery. And these are the things that you have to do.And pursue DFARS 252.204-7020 compliance
Remember that DFARS 252.204-7020 is a self-assessment using the DoD assessment methodology. This interim rule is in place today before CMMC is final. You have to do the self-assessment based on NIST 800-171 and use the DoD assessment methodology. You will generate a score and submit it to the DoD’s SPRS system. And you have to do that before CMMC is final. So, these are what you have to do before CMMC is out, so do not wait. Get CMMC consulting (a CMMC consultant) or CMMC help because you will possibly lose your contracts if you are not complying with these DFARS clauses.
DoD seeks to incentivize early CMMC compliance
[Paul] Right, that’s some sage advice, and that’s good to know. Well, recently, Kyle, we went to one of the DoD’s town hall meetings where the CIO’s office made a presentation and spoke about the current status of what was going on with the CMMC program; it’s essential to our CMMC consulting / CMMC consultant program. And they were looking at ways to incentivize the OSCs, the organizations seeking certification, to pursue certification before completing the rulemaking process. Can you speak a bit on that for a moment, please? [Kyle] Yeah. So, I think the DoD is still figuring out how to incentivize companies to do CMMC assessments early, especially CMMC 2.0 assessments, before Rulemaking. And what the DoD CIO mentioned is that they’ll incentivize by extending the timeline of the certification. If you get certified before rulemaking finishes, they won’t require you to do another certification until three years after the Rulemaking is complete.Early certification = cost savings
[Paul] All right, so they’ll extend the term, and that would represent a cost-saving to all of the OSCs because they wouldn’t have to – it’s not like they would have to pursue recertification within a strict three-year time frame, right? [Kyle] Yeah, although the details probably will come a little later. But that’s what we have heard from the DoD CIO.DoD Made CMMC Assessment Guides Available in November 2021
[Paul] Okay, the DoD recently released the assessment guides for level one and level two. Could you give a brief overview?CMMC Consulting and Scope Discussion
[Kyle] Yeah, scoping had always been a challenge before the CMMC 2.0 assessment guides. Because beforehand, there was confusion about what should be in scope. And does CUI’s scope only include IT? Or is it going to have some of the IoT or OT, the “Internet of Things,” or OT, the organization’s “Operational Technologies”?Five types of CUI assets
The DoD released the CMMC 2.0 assessment guides in late 2021. And it includes five different types of assets:
- CUI Assets: All the assets that process, transmit, or store CUI are CUI assets.
- Security Protection Assets: This category includes the hardware and software that protect CUI, such as firewalls, VPNs, and endpoint protection software.
- Contractor Risk Managed Assets: These are hardware & software that could store, process, or transmit CUI information. However, you have a policy option to say: “Thou shall not use the system to process, store, or transmit CUI information”! So, these are what they call: the Contractor Risk Managed Assets.
- Specialized Assets: These are government-furnished equipment, OT, operational technology, IoT or IIoT, the “Internet of Things” or “Industrial Internet of Things.” Test equipment – these types of assets are called “Specialized Assets.”
- Out of Scope Assets: And everything else that is not in scope, these are the Out of Scope Assets.
So, in our CMMC consulting / CMMC consultant / CMMC help program, when we document your scope, we want to identify these assets and document the people who have access to them.
We use our proprietary “CUI Data Lifecycle” approach to identify the CUI assets and what systems are processing, transmitting, and storing CUI information.
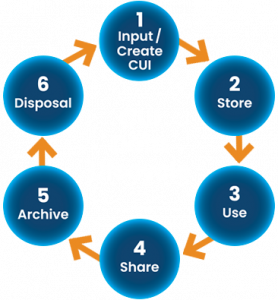
So, once we understand and discern your CUI Data Lifecycle, the people who have access to CUI become apparent, the systems that store CUI, and what systems touch CUI. And these will help you identify the scope of your CUI assets.
CMMC and NIST 800-171 don’t need to be company-wide
[Paul] That’s an excellent overview, and I know from the people who call us up weekly to seek our CMMC help in this area with NIST 800-171 and CMMC – they often feel like this is a company-wide exercise. That they apply to everybody, all the departments within the organization, but that’s not the case, right? You outlined that it’s just where CUI touches a company’s people, processes, and technology. [Kyle] Exactly. Not everybody within your organization needs to touch CUI, not all departments, especially for medium to large companies. Smaller ones might be an exception. But if you are a medium-sized company, you want to look into: Do the accounting department, marketing, finance departments, and HR departments need to touch CUI? If not, you don’t need to include these people, so try to reduce the CUI scope to as few people as possible. [Paul] Good advice for CMMC help. And folks will save money doing that, too. [Kyle] Exactly!Bifurcation and CMMC consulting / CMMC consultant
[Paul] Super! Okay, why don’t we talk about CMMC level two and “Bifurcation.” It’s an odd term; it’s not something I had heard much of before, but what is a bifurcation, and how does it mean how CMMC and NIST 800-171 are applied? [Kyle] Yeah, when the DoD initially released CMMC 2.0, they mentioned splitting level two. We’ll have two different types of certification requirements: Self-assessment for “Non-Prioritized” CUI, and you can do the self-assessment if you handle non-prioritized CUI. And you must have a third-party assessment by a C3PAO if you take “Prioritized” CUI. And what the DoD CIO mentioned in the town hall is that they don’t think they can distinguish the two, how to make it prioritized versus non-prioritized. If they can, there will be very few companies that will be qualified to do the self-assessment.I think they’re being very conservative, but essentially, most companies that have to have CMMC level two are required to get the independent third-party assessment from a C3PAO. So, maybe we don’t have to learn about bifurcation in our role as providers of CMMC help; as a CMMC consultant in CMMC consulting. But that’s what it means.
Plan on C3PAO assessment for Level 2
[Paul] Yeah, it sounds like it would be a big challenge just with what I’ve read about it. So, you know, that’s certainly good to know, and it seems like the prudent approach for the organization seeking certification would be to say: Hey, we need to plan in the future that we’re going to need a C3PAO assessment if we handle CUI. [Kyle] Yes, I think that’s a good approach. Assume that you will have to go through the independent assessment by the C3PAO. I think that’s the best assumption. The DoD CIO has not removed the word “bifurcation” for CMMC level two yet, so we cannot be apparent today about how bifurcation will work in the end or if they will remove it after the Rulemaking is complete. So, it remains to be seen. But from what we hear from the DoD CIO, bifurcation will not be applied to most companies that require CMMC level two.CMMC Consulting (CMMC Consultant) and inquiry letters
[Paul] Okay good. A couple of minutes ago, we talked about what the “Organizations Seeking Certification” should be doing now during the rulemaking process. So, we know from folks who contact us every week, the defense industrial base companies, that they’ve been receiving these letters from their prime customers and from the DoD that speak to or request where they stand – to know where they stand – concerning DFARS requirements.Going back to what you talked about earlier, performing the self-assessment and having an incident response plan in place. And they are submitting summary level information to the DoD’s SPRS web portal. Some folks are still struggling to do it. They either haven’t done it, or they’ve done it, but they don’t have much confidence in it because they just don’t have the expertise in this area. They need CMMC help. But we offer a service for these companies with a pretty quick turnaround, so I think it might be a good idea to talk about that.
CMMC Consulting (CMMC Consultant) service for SPRS submittal
[Kyle] Yeah. So, some companies, as you said, they have made the initial SPRS submission by checking off “yes” we have these practices implemented, or “no” we don’t have these NIST 800-171 practices implemented. And that’s all they have done. And they simplified their processes and overestimated their compliance level. So, they submitted a high score to the SPRS. And now come back to it knowing hey, this score may not be accurate, and we probably need to look at our scope. Take a look at our SSP because we just realized – hey, we don’t have the System Security Plan, and we don’t have the Plan of Action and Milestones. They need CMMC help.Low-cost CMMC consulting (CMMC Consultant) with a fast turnaround
So, when they contact us, we’ll put together a CMMC help proposal for them and do a CUI Data Lifecycle review. I mentioned earlier that we go through and understand their exact CUI scope and identify the CUI assets within their scope. We will help them create the System Security Plan or SSP based on each of the controls or practices of NIST 800-171. And we will identify the gaps they have, any gaps. We will document them in a Plan Of Action and Milestones and help them prioritize because you cannot do all of the gaps. You cannot remediate all of the gaps all at once.
Some of them are at a higher risk than others. Some of them will take a little bit more effort than the others. So, we will consider the risks and the amount of effort to put together the priority roadmap and help our customers, our clients, to help them get towards CMMC & NIST 800-171 compliance. We will help them submit or revise their SPRS score to reflect reality. We provide CMMC help so our clients improve their security scores and develop a good road map to move to CMMC and NIST 800-171 compliance.
Compliance foundation: NIST 800-171 self-assessment, POAM, and SSP
[Paul] Right, and this is pretty important too because that self-assessment is the starting point, the foundation of a compliance program. And so, it seems crucial that companies would want to know. They will want to get their bearings straight at the beginning of this before they start heading down the road. And not mistakenly think they’ve achieved compliance in some area, some practice area, but they haven’t met all the assessment objectives. [Kyle] Yeah, absolutely, and you know, they want to prioritize the work. And these companies will be busy with competing priorities. Some of their IT or security projects won’t align with what they need to do with NIST 800-171. So, we can look at their other projects and prioritize it with CMMC help. And to try to align some of the CMMC practices they can accomplish together with these other IT projects. We’ll try to align them and help them move more efficiently, you know, move towards CMMC. And make compliance a lot easier.KLC’s CMMC consultant / CMMC consulting prevents cyberattacks
[Paul] Right. And I think another thing I’d like to bring up right here, Kyle is the landscape of cyber threats and everything that’s going on today in the wake of, or I should say, the Russia-Ukraine war persists and drags on. We certainly hear in all the daily media accounts of cyber-attacks and cyber breaches that companies, not just defense industrial-based companies, but all companies in the US, are experiencing. And I know that we’ve recently begun prioritizing POAM remediation for the OSCs to give them CMMC help and strengthen their cybersecurity defense. And start there as they work toward compliance. [Kyle] So yeah. And yeah, if we see some of the deficiencies or the gaps are in two-factor authentication, you know, multi-factor authentication. Or the firewalls, the firewall rules are lacking. Or patch management is lacking. These fundamental practices will help companies defend against some of these cyber-attacks. So with our CMMC consulting / CMMC consultant, we will prioritize these practices and start implementing these practices as soon as possible because these are the high-risk items. Implementing these practices will not just give the companies a boost in the SPRS score, but in reality, they will be a lot more secure against cyber-attacks.CMMC Consultant and CMMC Consulting: The top 10 best cybersecurity practices
[Paul] Yeah, and that’s a great point. And I’m also going to put in a little shameless plug here. You’ve pulled together the best practice recommendations, currently in this cyber threat environment, from the Department of Defense, the NSA, the White House, and CISA. Let me see whom I am forgetting? [the FBI] I know there’s another one in there somewhere. But you’ve pulled all of these together. You’ve aggregated them to make it convenient for people to say look: These are the areas that folks should be focusing on first. And that these become part of the POAM remediation program. So, we can recommend that they follow those practices and strengthen their cybersecurity defenses against all of these escalating cyber-attacks. [Kyle] Yeah. So, these are the real threats that companies face today. We see more and more phishing, ransomware, and cyber-attacks against new and old vulnerabilities. So, these are the “10 Best Practices” that companies should apply to their environments right away to increase their defense. You know, to better enhance their security against cyber-attacks.CMMC Consultant and CMMC Consulting: Flowdown requirements explained
[Paul] Great stuff! We hear from our existing clients and the folks who call us up weekly. They have concerns about “Flow Down Requirements.” They’ve heard of the term. They recognize that somehow, it’s going to apply to them. If they have subcontractors, for example, who work for them, they need to ensure that their subcontractors are also compliant to the same level they need to be. Hopefully, I’m understanding and saying that correctly. But it might be helpful if you take a moment and speak to Flow Down Requirements. What the term means, and what do folks need to do to be complying.DFARS 252.207-7012 FLowdown
[Kyle] Sure, this is DFARS 252.207-7012, DFARS 252.204-7020, and CMMC. These are the rules, the clauses that require “Flow Down.” And what we mean by flow down is in most, if not in all of the DoD contracts that handle CUI, if CUI passes from the contractor to their subcontractors, it means the contractor needs to pass the exact requirement to protect CUI along to their subcontractors. And also, you know, all the subcontractors of the subcontractors, they must follow the exact needs to safeguard the CUI information. So, with DFARS 252.204-7012, if a company does not have CUI, if the subcontractors don’t get CUI from you, you don’t have to require them to follow DFARS -7012.DFARS 252.207-7020 Flowdown
The same thing applies to DFARS 252.204-7020. If your subcontractors don’t receive CUI from you, you don’t have to require they comply with DFARS 252.204-7020.
CMMC Flowdown
CMMC is different: CMMC or DFARS 252.204-7021. Suppose a subcontractor gets FCI or “Federal Contract Information” from you as a federal or DoD contractor. In that case, you need to require your subcontractors to get CMMC level one certification to meet the CMMC level one requirements. If you pass CUI information to your subcontractors, you will require your subcontractors to get the CMMC level two or level three. It depends on your level. But at the minimum, you will require them to get CMMC level two.
COTS Flowdown exception
COTS, “Commercially Off-The-Shelf” products are exempt. So, if you get commercially off-the-shelf products from your subcontractors, that subcontractor is considered a COTS vendor, [contractor], or subcontractor. They are exempt from all these requirements. If they are a COTS vendor, they are exempt from the DFARS -7012, -7020, and CMMC.
[Paul] Well, that’s interesting. So, even if you just focus on level one for a second. Even though they handle federal contract information, COTS allows them an exclusion, and it’s okay. They don’t even need to meet CMMC level one. [Kyle] That is correct. So, if you are a COTS vendor, you are exempt from CMMC or DFARS -7012 or -7020. To become COTS – it’s not a self-determination process – if you are a contractor and want to get the COTS vendor status, you have to get a “COTS Determination” from the DoD if you are a prime contractor. Suppose you are a subcontractor. You have to obtain a COTS determination form of approval from your prime contractors or the next level of subcontractors.COTS qualification criteria
[Paul] Okay, what are the criteria for becoming a COTS vendor? [Kyle] These companies have “Commercially Available” products. Their products must be commercially available and produced in a “Substantial Quantity.” And also, the products that you sell to the prime or the DoD cannot be “Modified” at all. So, if you qualify for these three, you most likely can become a COTS vendor. KLC provides CMMC help with COTSKLC’s CMMC Consulting (as a CMMC Consultant) for COTS exemption
[Paul] Right. And I know from the clients we’ve given CMMC help in this area. I mean, I should back up for just a second and say: We have a service that provides CMMC help in this area, so if they believe they are a COTS vendor right, they need to get an approval, an exemption; either from the DoD or from their prime customer. And from what I understand, you know, working with the clients past, we go through a process similar to preparing a legal case?We’re documenting their products and showing the DoD or the prime customer’s contract officer that it meets the particular FAR and DFARS requirements. And it seems, Kyle, like we’re making the contract officer’s job easy for them to say: “Ah, okay, you check all the boxes. Everything seems to be in order here. It’s a commercial item, and it is a COTS item. You don’t need to worry about NIST 800-171 and CMMC.” Something like that, right?
Commercially available, in substantial quantity, and with no modifications
[Kyle] Yes yeah, absolutely so, there’s a process to determine COTS. So, if the company is COTS, it must meet the three criteria: Is it commercially available, and are they producing substantial quantities? We will have to look into your competition and document some of the competing products right. If you say “substantial quantity,” we’re going to do market research and identify what you mean by substantial quantity: how many companies are producing these, right. And also, you cannot modify it.We provide CMMC help by looking into the products you sell to your prime or the DoD: Are they being “modified” or “configured” because there is a fine line. We’ll provide CMMC help to determine if you are qualified to become a COTS vendor. So, initially, we will assess to see if you are likely to become a COTS vendor. When talking to your prime and the DoD, if it is unlikely for you to get the COTS status, we’ll suggest you move towards complying with CMMC or NIST 800-171. But if you are indeed qualified for COTS, we provide CMMC help with putting together the determination form and help you submit it to the prime or the DoD. You know, it makes the process a lot easier for you.
COTS case studies with clients we’ve performed CMMC consultant and CMMC consulting
[Paul] Right. And I should say that we have a couple of case studies with two clients in this area. And they’re available on our website, so I’ll put the link here when we finish this CMMC Consulting Video. So, that’s very good, that’s all very helpful, right. [Kyle] Yeah, if you receive compliance request letters from the primes, they don’t distinguish if you’re a COTS vendor. So, if you know you’re a COTS vendor, we want to provide CMMC help with putting together a convincing package that you can share with your primes and DoD. [Paul] Right. Now that’s great, and, you know, these engagements are a reasonably quick and low-cost consultation. But, you know, Kyle, for these two manufacturers, right, I think in these two cases, they saved themselves a six-figure, a likely six-figure compliance program budget, and they don’t have to do that, so it makes things quite a bit easier. [Kyle] right.Incident Response Requirements DFARS 252.204-7012
[Paul] Kyle, we should also talk about the “Incident Response Plan” requirements of DFARS 252.204-7012. Yes, it’s doing the self-assessment and having an incident response plan. But there’s an additional requirement with the DoD: To be able to report a “Cyber Incident” when they occur. So, maybe if you could talk to us about incident response plans, what does a good one look like, and what does an OSC need to do to be able to report an incident to the DoD, please?72-hour reporting requirement
[Kyle] Yeah, absolutely. We’re referring to DFARS 252.204-7012. There is an incident reporting requirement. If you experience an incident, you have to report it to the DoD within 72 hours of the discovery. It’s not saying that you have to figure out everything, get everything all done and submit the entire report to the DoD within 72 hours. The DoD only requires you to report that you have found a security incident. And you have to notify them saying we found this problem, we discovered this type of incident, at “this” time of discovery, right. So, these are the types of information that the DoD wants you to report to them within the first 72 hours of discovering the incident.ECA certificate requirement
Yeah, you also want to get an “ECA” certificate, which is required. But if you already have a “CAC” [“common access card”], you don’t have to get an ECA certificate. Or sometimes, they call it a “Medium Assurance Certificate.” You need to have that certificate to report an incident to dib.net, the DoD website for reporting incidents to the DoD. Suppose you don’t have the certificate; you cannot notify the DoD. So, these are some things we’ll help our clients get an ECA certificate as well, right.
An effective Incident Response Plan instills confidence
So, you want to have an incident response plan because, in the event of the incident, it’s going to be very stressful already if you don’t have a plan in place. You will struggle to know what to do. Next, it won’t be easy. And most likely, you’re going to miss a few steps and do some things that you probably are not supposed to. And you are likely going to forget to report to the DoD. You will be violating the DFARS -7012 clauses. So, you want to prepare by putting together a security incident response plan. And our CMMC consulting as a CMMC consultant services help you in this area.
CISA Shields Up alert
As we mentioned earlier, the frequency of security incidents is getting higher. CISA issued a “Shields Up” alert, along with the NSA. They published the Shields Up alert. The White House also announced a recommendation to increase your protection awareness about ransomware attacks. So, these are the things that we should keep in mind. If you already have an incident response plan, you have to ensure your staff understands how to follow the incident response plan once you release it.
Incident Response Tabletop Exercises improve readiness
And also, you want to conduct a regular exercise, you know, at least once or twice a year. So, what we call “Tabletop Exercises” is a walk-through.
A scenario may be: There is a ransomware attack on “this” day. So, you get all the critical stakeholders like IT, HR, Security, Compliance, Legal, and say – here’s an incident at 7:02 am. What do you do? And we’ll help you walk through this exercise and see if your incident response plan is indeed effective. If it is ineffective in certain areas, our CMMC consultant / CMMC consulting service will help you document a plan recommending improvements to your incident response plan. And make sure that, you know, we identify for the key stakeholders, some of the areas and some of the responsibilities that are not clear. That will help you improve and enhance your incident response plan.
Our experience with an unprepared client
[Paul] And to that point, Kyle, I’ve seen it with some of the clients that we help. I can think of one in particular with the Microsoft Exchange Server issue several months ago. When this happens and a company doesn’t have a clear IRP in place, it’s very stressful because folks are anxious and concerned. They’re not sure what to do. They know something has happened; their data is at risk. But it’s a very stressful and crazy environment at that point. And people are trying to get a handle on it. And then they often don’t know. They don’t know whom to call. Where to report? Are there customers that need to be made aware of this? Or do they call the FBI?Folks often don’t know, so this is one of our services: Helping clients develop an incident response plan. Our CMMC Consulting options (as a CMMC Consultant) include tabletop exercises. From the clients we’ve worked with, I know that they found it very valuable. And it’s like okay, now if something happens, they feel like they’re much better prepared to handle it and deal with it: they know what to do. They know whom to call, and it just restores confidence. They feel much better about it.
Call the FBI?
[Kyle] Yeah, absolutely so, since you just mentioned the FBI: you want to let people know when to contact legal and law enforcement in what situations. So, there should be a procedure because, for example, if you call the FBI, whatever you said to them, you cannot take back, right. So, whatever you report to the FBI, it becomes a federal case. You cannot just say: I was “just kidding.” I want to take the case back. It’s not going to happen because the FBI will take its course of action. [Paul] And I mean, too, if you get hit with a ransomware attack, people will wonder, should we pay this? Do you know how much of my data is corrupt? How badly do I need it? You know, can I trust the cryptocurrency? Etc. And it just, I’ve learned from watching you conduct these tabletop exercises that it’s very enlightening. And it’s very worthwhile to have a good incident response plan in place. I mean, not only is it the requirements under DFARS -7012, but it’s just its good business practice. And in today’s threat environment, everything that’s going on makes perfect sense.Good versus inadequate Incident Response Planning
[Kyle] Yup, absolutely. And you can tell when a company has good incident response versus inadequate incident response planning. We help companies deal with incidents quite often. And we see it when people don’t have a good incident response plan when you show up. It’s like: “Show me the log?” They’ll say: “What log?” And “How many days of a log do you have?” They say: “Three days.” And, you know, they’ll not be able to get a lot of the information back. And yeah, that’s unfortunate. Or, it will take a lot longer to find out exactly what’s going on and deal with some of these incidents. And yeah, you want to have a good incident response plan. Especially I would say, for ransomware. These days ransomware is pretty standard. And I’ll say that people need a good incident response plan, especially for ransomware.CMMC Consultant/ CMMC Consulting for CUI marking and labeling
[Paul] Kyle, another area where we get a significant number of calls is “CUI Marking and Labeling.” And, you know, we offer training in that area, but this seems to be a big issue for many companies.I’m not sure if they’ve thought that much about it. Because if you believe, for example, that if you’re not presently NIST 800-171 or CMMC compliant. And you’re receiving CUI information from multiple sources. You’re getting it in email, and then you might be forwarding it in email. And then it’s stored on the server, and then possibly it’s in Gmail.
But it could be in multiple locations spread throughout a company’s information system. And so, there’s a whole process behind identifying it, inventorying it, and then going back and marking and labeling it. And then developing templates and possibly an automated solution to help when CUI comes into the organization. But could you talk a bit about that? The aspects of compliance for NIST 800-171 and CMMC about CUI marking and labeling?
Some Federal agencies don’t get it right either
[Kyle] Right, yup. CUI marking is still pretty confusing and is a rather complex problem. And it does start with the government because the government doesn’t label everything that is CUI. When you are talking to contract officers you can, you might ask them: Why don’t you mark these as CUI?They probably will tell you, okay. Yes, we will work on it, but it might take a long time for the agencies you work with to start marking things correctly.
Sometimes they don’t have marking, but that doesn’t mean that you, you know, that doesn’t mean that you should not protect this type of information. So, it becomes a little bit of a challenge because you have to figure out what type of information is CUI. Right, and also the CUI that you create, you need to mark them as CUI. So, how do you mark it? That’s become a challenge as well.
All types of electronic CUI files require CUI marking and labeling
And these are not just Word documents but also PDFs, Excel spreadsheets, PowerPoint presentations, and some of your drawings from your CAD programs. And emails, so it’s not an easy problem to solve. With KLC’s CMMC consulting and CMMC consultant service, we have people that specialize in helping our clients put together a CUI marking strategy.
We use data loss prevention techniques and some other solutions to help you label CUI properly. We can help you create some templates you will be able to use for your most common types of CUI. Specifications and notifications, distribution notification statements, or some of the dissemination controls – we can help you put together common CUI banners that you should put on your CUI files. So, these are the things that we can help you put together and help make it a lot easier for you to handle and deal with the CUI marking and labeling.
KLC’s CMMC Consulting as a CMMC consultant includes training
We’ll also help you do CUI marking and labeling training because you need to ensure that your company’s staff understand how to read and label your CUI information properly. Identify who has the responsibility when staff isn’t clear, who they turn to, and ask for help with this type of information. So, these are the things that we can help you put the training together for your company.
Kyle Lai, CMMC Provisional Assessor, and Instructor
[Paul] Right, and I think that’ll be the subject of another CMMC Consulting Video. But certainly, there are training requirements. Your abilities as a CMMC Provisional Assessor and Provisional Instructor, together with your credentials and experience in this area, make you a true expert when it comes to all things with CMMC and NIST 800-171. And so, we do offer these training services to our clients as well. And Kyle, I’m also going to link to a CMMC Consulting Video that we did earlier with Carl Johnson, one of our colleagues that we bring in to help with this type of work. Folks may find that interesting to listen to and should also check out. [Kyle] Yes, absolutely.KLC provides CMMC consultant and CMMC Consulting as a cleared C3PAO candidate
[Paul] Okay, Kyle, this was terrific! Good discussion! I think people will find it helpful. And we should wrap it up by saying: KLC Consulting – we’ve been in business since 2002. We’ve been working in this area, DoD cybersecurity, dating back to 2010. And we’ve slowly been working our way toward becoming a specialist in DoD cybersecurity. We decided to pursue becoming a C3PAO organization. We’re a cleared candidate with the CMMC-AB. We need to complete our DIBCAC assessment and become level two ourselves.But we anticipate that happening probably over this Summer or early Fall. And so, our niche specialty, if you will, is helping defense industrial-based companies become NIST 800-171 and CMMC compliant. And we do that by providing the most affordable consulting and technology solutions available today. So, we hope you find this CMMC Consulting Video interesting. And if you have any questions about CMMC, NIST 800-171, cybersecurity training, the CMMC assessment guides, or any of the topics we covered today, I highly encourage you to give us a call. You can find our contact information on that section of our webpage, and we hope to hear from you soon. So, thank you very much!
CMMC Consulting
Help with NIST 800-171 and CMMC Compliance
KLC Consulting’s DoD cybersecurity experts coordinate with your team to support all areas of NIST 800-171 and CMMC. Let’s get you to “CMMC Assessment Ready!”